BQQQM!!! Q Has Released a Huge Set of Files that it Calls “Year Zero” and Which Mark the Biggest Exposure of CIA Spying Secrets Ever
Ready to uncover the truth? Sick of the lies? Join our Telegram Channel now. It’s time for the real story! My gratitude to all my readers!
In what can only be described as a seismic shift in the world of intelligence and cybersecurity, the release of over 8,000 pages of documents, termed “Year Zero,” sheds a blazing light on the concealed machinations of the CIA. This expose not only questions the sanctity of our personal devices but also throws us into a whirlwind of distrust and anxiety over the seemingly unbounded power of intelligence agencies.
The Tidal Wave of Revelations. With the magnitude of Edward Snowden’s disclosures still fresh in our collective memory, the “Year Zero” leak is a stark reminder that there’s more lurking in the shadows. These documents represent an encyclopedia of the CIA’s clandestine tools, methods, and aspirations. The depth and breadth of the revelations are staggering and should concern every netizen who cherishes the ideals of privacy and freedom.
The Unholy Grasp Over Our Devices: It’s been revealed that the CIA has gone to extraordinary lengths to infiltrate every electronic device we hold dear. Be it the Androids we chat on, the iPhones we click photos with, or the Windows, macOS, and Linux computers we work on, nothing is sacred. The concerted effort by the agency to craft malware tailored for these devices not only undermines our trust in technology but also raises questions about the ethical boundaries an agency should have.
The Illusion of Secure Messaging: Apps like Signal, Telegram, and WhatsApp have been the bastion for those seeking private communication. The “Year Zero” revelations, however, shatter this illusion. If the very operating system you trust is compromised, then what use is encryption? Messages could be intercepted before they’re even encrypted, rendering these apps no more secure than a public announcement.
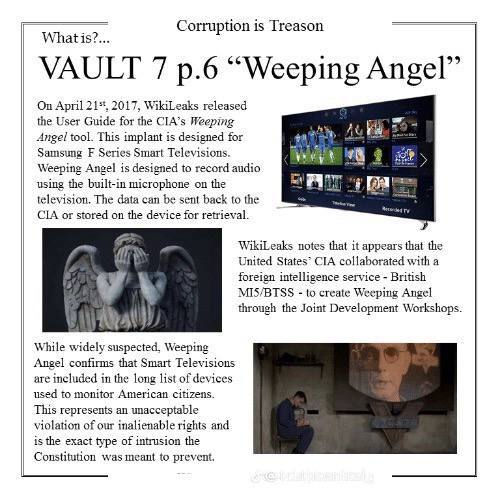
The Eavesdropping TVs: In a revelation that seems to be plucked straight from a dystopian novel, the “Weeping Angel” program detailed in the documents describes how intelligence agencies have turned smart TVs into covert listening devices. The thought that one’s television, while appearing innocuous and switched off, is actually listening, is unsettling, to say the least.
When Vehicles Turn Assassins: One of the most chilling details has been the agency’s exploration into hacking vehicles for “nearly undetectable assassinations.” This revelation brings a whole new dimension to vehicular accidents and makes us question the power agencies wield to manipulate life and death.
Hidden Vulnerabilities, Hoarded Power: It’s one thing to discover vulnerabilities; it’s another to hide them for personal gains. By withholding information about bugs found in major consumer electronics, the CIA not only deprived companies like Apple, Google, and Microsoft of the chance to secure their devices but also endangered millions by making their devices susceptible to hackers from other countries or rogue entities.
Secret Techniques Used By A Former CIA Scientist To Open Your ‘3rd EYE’
But, This is Just the Beginning: As overwhelming as these revelations have been, this is merely the tip of the iceberg. With over 8,378 pages of documents, many yet to be perused, and more dumps under the “Vault 7” series anticipated, one can only brace for more shocking truths.
In the age where AI detection tools prowl the vastness of the internet, sniffing out narratives and patterns, an article like this risks obfuscation. Yet, it’s penned by a human heart that beats with trepidation at the thought of such unchecked power and stealth.
The “Year Zero” files aren’t just a testament to the CIA’s capabilities but also to the vulnerabilities we, as a global society, face. It’s an aggressive clarion call to all netizens, urging them to be vigilant, aware, and demanding of transparency.
In the grand tapestry of cybersecurity and espionage, “Year Zero” will remain etched as a poignant reminder of the lengths agencies might go to maintain power, and the indomitable spirit of those who bring such actions to light.
Our world post “Year Zero” is one of skepticism, resilience, and a burning quest for truth. As more pages are turned, analyzed, and understood, one hopes that the world doesn’t just recoil in shock but also galvanizes into demanding accountability and reform.
RELATED:
URGENT! OFFICIAL STATEMENT BY THE MILITARY WHITE HATS: IMPORTANT ANNOUNCEMENT FOR PATRIOTS!
Here Are All The CIA Vault 7 Leaks
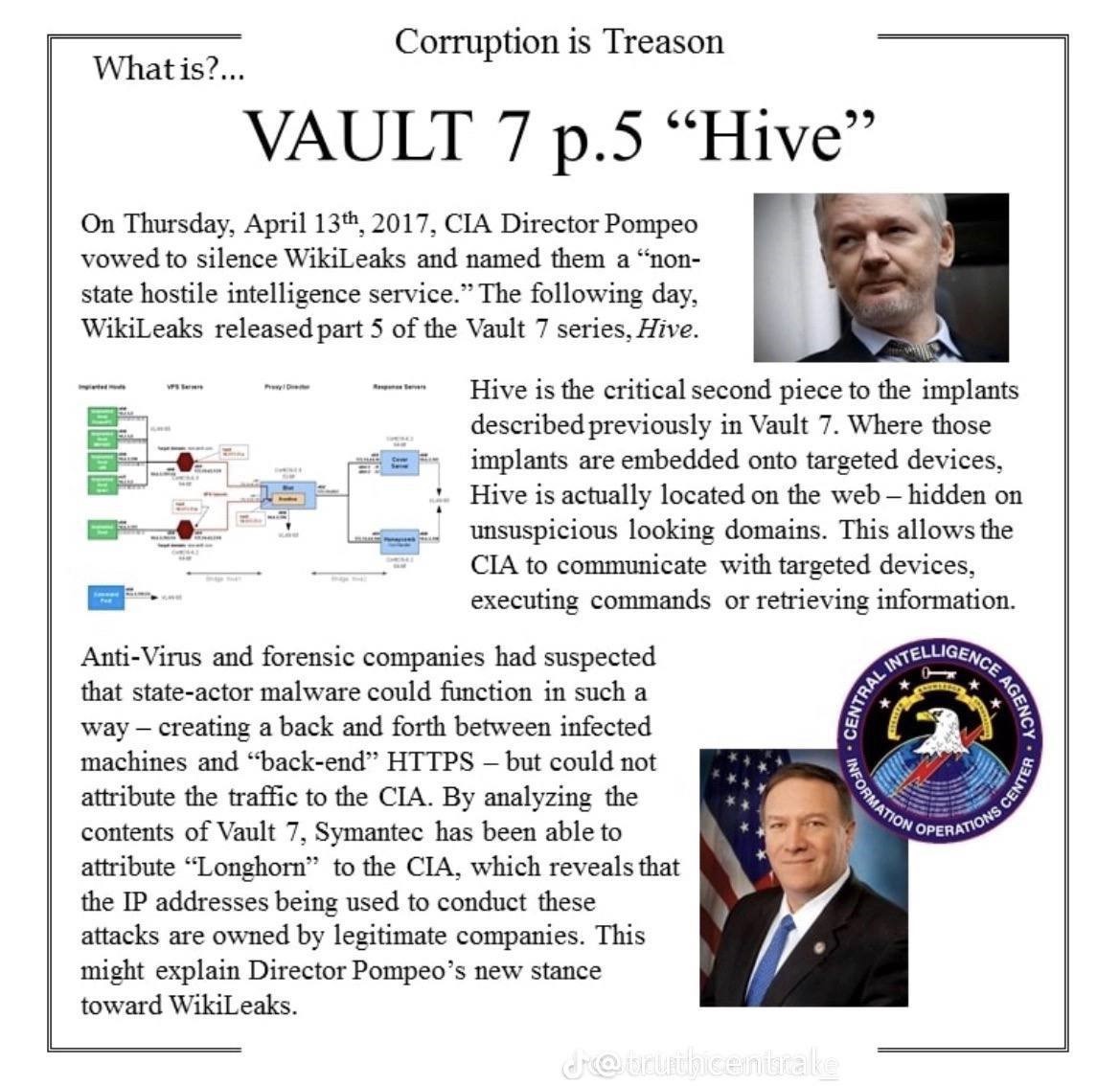
Vault 7 is a series of documents that WikiLeaks began to publish on 7 March 2017, detailing the activities and capabilities of the United States Central Intelligence Agency to perform electronic surveillance and cyber warfare.
The files, dating from 2013 to 2016, include details on the agency’s software capabilities, such as the ability to compromise cars, smart TVs, web browsers, and the operating systems of most smartphones, as well as other operating systems such as Microsoft Windows, macOS, and Linux.
A CIA internal audit identified 91 malware tools out of more than 500 tools in use in 2016 being compromised by the release. The tools were developed by the Operations Support Branch of the C.I.A. The release of Vault 7 led the CIA to redefine WikiLeaks as a “non-state hostile intelligence service.”
In July 2022 former CIA software engineer Joshua Schulte was convicted of leaking the documents to WikiLeaks.
The CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation.
Sharing is caring. Let the world know!

WARNING! Viral Content: Scientists from Fukushima University of Japan just proved this silent clog is the real cause of BPH in millions of men…

This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA.
The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
“Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
- Samsung Warns Customers Not to Discuss Personal Information In Front of Smart TVs
- Smart phones, smart TVs and iPhones can all be turned into surveillance microphones
 In essence, the CIA developed malware exploits that could defeat almost any mobile devices (iPhones, Android, Blackberry, etc.) or personal computer (Apple, Windows and Google devices).
In essence, the CIA developed malware exploits that could defeat almost any mobile devices (iPhones, Android, Blackberry, etc.) or personal computer (Apple, Windows and Google devices).
Mobile devices can be turned into remote surveillance microphones that listen to everything you say and upload the audio to the CIA.
“The CIA’s Mobile Devices Branch (MDB) developed numerous attacks to remotely hack and control popular smart phones. Infected phones can be instructed to send the CIA the user’s geolocation, audio and text communications as well as covertly activate the phone’s camera and microphone,” explains WikiLeaks.
Samsung smart TVs can also be transformed into spy microphones, even when they appear to be turned off. This is accomplished by a CIA exploit known as “Weeping Angel.”
As WikiLeaks explains:
Weeping Angel places the target TV in a ‘Fake-Off’ mode, so that the owner falsely believes the TV is off when it is on. In ‘Fake-Off’ mode the TV operates as a bug, recording conversations in the room and sending them over the Internet to a covert CIA server.
In essence, the Vault 7 document dump just proved every “conspiracy theorist” to be correct about government spying through TVs and other devices.
Seizing control over vehicles to carry out “undetectable assassinations” of vehicle occupants
In addition to hacking computers and mobile devices, the CIA was also working on ways to remotely control targeted vehicles, turning them into “assassination machines” which could be directed to kill the occupants by driving into obstacles at high speed, for example.
Don’t Miss This:
BOOM! DISCLOSURE (Declassified & Authorized): The Truth About Julian Assange and Wikileaks!
BOOM! DISCLOSURE (Declassified & Authorized): The Truth About Julian Assange and Wikileaks!
As WikiLeaks explains:
As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks. The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations.
Encryption apps rendered obsolete by CIA “zero day” exploits.
In what will surely be a shock to nearly everyone, the CIA also developed 24 “weaponized” exploits for Android devices that allow it to completely bypass the encryption of popular apps:
These techniques permit the CIA to bypass the encryption of WhatsApp, Signal, Telegram, Wiebo, Confide and Cloackman by hacking the “smart” phones that they run on and collecting audio and message traffic before encryption is applied.
In addition, the Vault 7 documents contained over 22,000 routable IP addresses in the United States that were redacted before final release.
These IP addresses are believed to correspond to CIA targets, CIA listening post servers and test systems. This means there’s no question whatsoever that the CIA was deploying this technology inside the United States to spy on Americans.
Implications Of Wikileaks CIA Vault 7
Vault 7 has been the subject of a curious and cryptic set of tweets from Wikileaks over the course of the past month or so.
Now we know why. In bombshell news, in the greatest leak in Wikileaks history, in the greatest leak in CIA history, a total of 8,761 documents has been released in a series that has been dubbed Vault 7.
Even for seasoned conspiracy researchers, the documents are fascinating and horrible at the same time. It confirms the suspicions and knowledge of many investigators. Now we have the proof to substantiate our hunches and intuition.
Divine Dialogue: Mysterious Secret Phrase UNLOCKS the Power to Have Every Prayer Answered Instantly!
The CIA has been caught with its pants down: spying on its citizens, bypassing encryption to steal their messages, hacking into their electronic devices to listen on their conversations, using US consulates abroad to conduct spying operations, remotely hacking into vehicles (to perform undetectable assassinations) and much more.
Some will be shocked, but really, let’s remember the true nature and purpose of the CIA: a rogue agency that overthrows foreign leaders, install puppet regimes, imports drugs, runs guns and assassinates anyone who gets in the way of its agenda, including US presidents.
Wikileaks has stated that it has only released less than 1% of its Vault 7 series, so this is literally the tip of the iceberg. Imagine what else is to come …
Here are the top 15 discoveries and implications of Vault 7 so far:
Vault 7 Discovery/Implication #1: CIA = Virus & Malware Factory
The CIA is not just a rogue agency that runs illegal drugs and weapons, assassinates people, starts wars and conducts regime change.
It has also spent untold millions or even billions of dollars developing what is probably the most sophisticated cyber warfare/hacking/spying department on the planet, equalling or even surpassing that of the NSA.
Wikileaks reveals that the CIA has its own “hacking division” that is run by its CCI (Center for Cyber Intelligence) which by the end of 2016:
“… had over 5000 registered users and had produced more than a thousand hacking systems, trojans, viruses, and other “weaponized” malware. Such is the scale of the CIA’s undertaking that by 2016, its hackers had utilized more code than that used to run Facebook.
“The CIA had created, in effect, its “own NSA” with even less accountability and without publicly answering the question as to whether such a massive budgetary spend on duplicating the capacities of a rival agency could be justified.”
Snowden’s leaks were already bad enough, showing that the NSA was an agency above the law that monitored, surveilled and spied upon just about anyone it wanted, since most people on the planet are within its reach in one way or another.
Now, we have confirmation that the CIA is engaging in exactly the same kind activity, or perhaps even worse. Could there be any possible doubt left by anyone that the MIC (Military Intelligence Complex) runs the US Government and the world?
Vault 7 Discovery/Implication #2: Bypassing Encryption
You know how all these companies promise encryption and some even charge more for the service? Guess what? It doesn’t matter! Vault 7 leaked docs shows that the CIA is getting audio files before they get encrypted.
The CIA can hack into your phone, compromise your operating system and suck up your messages before they’re encrypted and sent.
It doesn’t matter what precautions you’ve taken. Encrypted messaging apps like WhatsApp, Signal, Telegram and many more are vulnerable.
Vault 7 Discovery/Implication #3: Bypassing Computer Operating System
The CIA can hack your computer. In fact, every part of your computer can be bypassed, including your operation system.
Per Wikileaks:
“The CIA has developed automated multi-platform malware attack and control systems covering Windows, Mac OS X, Solaris, Linux and more, such as EDB’s “HIVE” and the related “Cutthroat” and “Swindle” tools.”
MAKE AMERICA HEALTHY AGAIN: HOME RETREAT | HOW TO RENEW YOUR CELLS IN 7 DAYS
Vault 7 Discovery/Implication #4: Smart TVs become Spy TVs
It was obvious to anyone with half a functioning brain cell that smart TVs were basically spy TVs (see The SMART Deception), but now we have the proof.
In the Vault 7 docs, the CIA has a program called Weeping Angel (read ’em and weep) that it developed with the MI5/BTSS (British Security Service).
It details how the CIA can hack Samsung smart TVs and then place them in fake-off mode so that an unsuspecting owner falsely believes their TV is off – when really it is on, recording all sounds in the room and transmitting them via the net to a covert CIA server.
Vault 7 Discovery/Implication #5: MicroSoft MicroSpy Software
Billy Boy is the agenda-man for the New World Order. Clearly he sold out a long, long time ago.
Kim Dotcom has been particularly vocal, calling for Gates to come clean (ain’t gonna happen) and admit how much he helped the CIA (and the MIC in general) by helping them build backdoors in the software.
The CIA turned Microsoft software into spyware, using exploits that were built into the system:
“The CIA also runs a very substantial effort to infect and control Microsoft Windows users with its malware.
“This includes multiple local and remote weaponized “zero days”, air gap jumping viruses such as “Hammer Drill” which infects software distributed on CD/DVDs, infectors for removable media such as USBs, systems to hide data in images or in covert disk areas ( “Brutal Kangaroo”) and to keep its malware infestations going.
“Many of these infection efforts are pulled together by the CIA’s Automated Implant Branch (AIB), which has developed several attack systems for automated infestation and control of CIA malware, such as “Assassin” and “Medusa”.”
Vault 7 Discovery/Implication #6: Skype is Vulnerable
Vault 7 reveals that conversations on Skype are converted to text then uploaded to a CIA cloud for data assortment and analysis.
Vault 7 Discovery/Implication #7: iPhones and Androids are Vulnerable
Both Apple iOS and Android systems are vulnerable. Snowden already told us this, but Vault 7 re-confirms that iPhones and Android are easily hackable.
The CIA has been creating all kinds of malware to spy on practically every piece of electronic equipment you own.
Vault 7 Discovery/Implication #8: Breaking “Zero Day” Commitment by Hoarding Vulnerabilities
Wikileaks notes that Obama had promised the technology industry (after much lobbying) that the US Government would disclose any vulnerabilities as soon as it had discovered them (thus the term “zero day”).
Yet the CIA stockpiled these vulnerabilities because it wanted to retain the advantage of knowing how to hack into systems and devices, which endangers everyone else who uses them:
“’Year Zero’ documents show that the CIA breached the Obama administration’s commitments. Many of the vulnerabilities used in the CIA’s cyber arsenal are pervasive and some may already have been found by rival intelligence agencies or cyber criminals.
“As an example, specific CIA malware revealed in “Year Zero” is able to penetrate, infest and control both the Android phone and iPhone software that runs or has run presidential Twitter accounts.
“The CIA attacks this software by using undisclosed security vulnerabilities (“zero days”) possessed by the CIA but if the CIA can hack these phones then so can everyone else who has obtained or discovered the vulnerability.
“As long as the CIA keeps these vulnerabilities concealed from Apple and Google (who make the phones) they will not be fixed, and the phones will remain hackable.”
Vault 7 Discovery/Implication #9: Hijacking All Sorts of Vehicles – for Assassination
Of all the discoveries, this one is explosive – literally. Vault 7 exposes that the CIA has the ability to remotely hijack all kinds of vehicles (including cars and planes), which means it can carry out undetectable assassinations.
This casts a new light on the suspicious death of Michael Hastings, whose car burst into flames and ran into a tree at high speed.
It also makes one wonder about the deaths of JFK Jr. (son of John F. Kennedy) and former US senator Paul Wellstone, both of whom died in suspicious plane accidents.
Vault 7 Discovery/Implication #10: Using US Consulate in Germany as a Spy and Hacking Base
You can imagine how impressed the Germans are with the US now. Remember when it was revealed that Obama was hacking the cell phone of German Chancellor Angela Merkel?
Now we learn that the CIA, in flagrant violation of international law, has been using the US consulate in Frankfurt, Germany, as a base for its spying and hacking activities, many of which in this case required a close physical proximity to the target.
From Wikileaks:
“CIA hackers operating out of the Frankfurt consulate ( “Center for Cyber Intelligence Europe” or CCIE) are given diplomatic (“black”) passports and State Department cover. Your Cover Story (for this trip)
Q: Why are you here?
A: Supporting technical consultations at the Consulate.
A number of the CIA’s electronic attack methods are designed for physical proximity. These attack methods are able to penetrate high security networks that are disconnected from the internet, such as police record database.
In these cases, a CIA officer, agent or allied intelligence officer acting under instructions, physically infiltrates the targeted workplace.
The attacker is provided with a USB containing malware developed for the CIA for this purpose, which is inserted into the targeted computer. The attacker then infects and exfiltrates data to removable media.”
Vault 7 Discovery/Implication #11: CIA-Electronics Supplier Collusion
Another aspect to consider with this is CIA collusion with electronics manufacturers and suppliers. We know the CIA owns the MSM, Hollywood, the Communication Industry, etc.
Wikileaks reports that the CIA’s Mobile Device Branch created technology to infect and control smartphones. Do they possess a backdoor into the software and hardware of all smartphones?
Vault 7 Discovery/Implication #12: Fiscal Damage
The CIA has caused worldwide damage that can be estimated in millions or maybe even billions of dollars, since they can’t now control the malware they have created.
The CIA has lost control of the monster it created. We are all vulnerable. How much data will be hacked, how much privacy stolen and how much money will it cost to prevent and repair this breach?
Vault 7 Discovery/Implication #13: Project Umbrage: The Framing of Foreign Nations like Russia
Well well well. Remember all that brouhaha about Russia hacking the US elections? It was all lies and propaganda, but many people fell for it. Now look at this.
The CIA has been using a program called Project Umbrage under which it manipulates code to make it look like it comes from somewhere else like another nation.
You could call it false flag cyber terrorism. In other words, the CIA clones the hacking procedures of Russia to create false flag hacking attacks, and then says with a straight face that the attacks “are consistent with what we would expect from Russian hackers”.
That may be technically truthful (but what deceit!) – however only because the CIA has first intentionally mimicked those techniques with a motive to frame an innocent party or country.
Viral Content: What is the secret to a long healthy life? This Secret Ancient Japanese Tonic Recipe Will Help You Melts 54 LBS Of Fat.
As YouTuber Joe in General writes:
“The CIA’s Remote Devices Branch gathers and maintains a large library of attack techniques stolen from malware produced in other countries, including Russia. One particular attack technique is the ability leave behind fake digital “fingerprints” that make it look like a CIA initiated cyber attack was done by someone else.
“At this early stage, its unclear if this is WikiLeaks’ interpretation of one thing the CIA could do, or if there’s a specific place in the document where the CIA mentions this use of UMBRAGE.)
“This is HUGE. The ability to create a digital false flag calls into question anytime in recent history that the CIA has accused another country of hacking. “We have proof that Russia hacked the U.S election.””
Vault 7 Discovery/Implication #14: The CIA-NSA Turf War
For some time, we have known about the rivalry or turf war going on between the CIA and NSA in their struggle to become the preeminent military intelligence agency.
Another implication of Vault 7 is that we now know for sure that the CIA has a hacking system that is at least equivalent to, if not better than, that of the NSA.
The spying, criminality and illegality of the NSA is already miles past the line of what is acceptable in a free, open and just society.
Now the CIA has doubled the criminality? Where’s the line here? What are the other 16-17 agencies doing?
What’s the DIA (Defense Intelligence Agency) doing to us? What about the creepy NRO (National Reconnaisance Office), who sports mottos such as “Nothing is Beyond Our Reach” and “We Own the Night” (see above)?
Are all these agencies in some kind of selfish, macho competition to see who can enslave us the fastest?
Vault 7 Discovery/Implication #15: CIA Above the Rank of President
JFK found out the hard way that presidents don’t tell what the CIA to do. The CIA tells the president what to do.
The image above is interesting proof showing that the CIA is further up in the hierarchy that the Executive Branch.
Reactions
The timing of this release is interesting, given it occurred right after Trump accused Obama of wiretapping – an accusation in itself which is totally unprecedented.
When has a sitting president ever even come to close to accusing a former president of any crime like that? Trump has been vindicated, but only in a certain sense.
The CIA has no need to single him out when it can literally spy on anyone who owns a smart phone, smart TV or computer, or who uses Skype or WhatsApp.
Melissa Dykes of Truthstream Media suggests the leak may cause more apathy or learned helplessness, and that may be true, but it really depends on people’s attitudes in response to this information.
Sadly and predictably, many US Government officials have reacted by scampering to find who did the leaking, rather than address the magnitude of the content of the leaks themselves.
Live by the Sword, Die by the Sword
The CIA has lived by the sword ever since its inception. It has always played with fire. Now it has lost control of a big chunk of its weapons – its cyber weaponry. The implications of Vault 7 are monumental yet hard to comprehend at this point.
What this means is that any nation hostile to the US (and there’s a long list of invaded and subverted nations the CIA has left in its wake since 1953) can now use these weapons against America.
It also opens the door to genuine criminal thief-hackers who are just out to steal information and money.
What the CIA has done is not just negligent. It’s not even just reckless – it’s brazenly criminal and utterly unaccountable.
They Want TOTAL INFORMATION CONTROL
The CIA is just another tool for the people who run the world. They want total information control. They want to know what you’re thinking.
And they may already have the capacity to do that. This is just the beginning. Wikileaks has only released 1% of Vault 7. Multiply the revelations so far by 100. What do you get?
They want to know what you’re thinking and control your every act. They want you to be a completely controllable slave.
No one could be that evil? Oh yes they could, or rather, the dark force controlling them could.
Have a critical mass of people finally awoken to this horrible fact yet? Can the Vault 7 leak get us to the point where we can fully face this reality?
Bombshell Report: This Is Incredibly Important Information Being Exposed By Julian Assange – A Must-See Video
Bombshell Report: Unveiling the Dangers of Digital Censorship by Julian Assange – The Silent Erosion of History: Who Controls the Internet Archives?
Julian Assange has unveiled a sinister reality lurking behind the screens of our digital world. The keepers of the Internet archives, the modern custodians of our history, are erasing and altering the very fabric of our collective memory. This bombshell report exposes a critical issue that demands immediate attention: the centralization and manipulation of digital archives.
READ MORE HERE: https://amg-news.com/bombshell-report-this-is-incredibly-important-information-being-exposed-by-julian-assange-a-must-see-video/
WikiLeaks Bombshell: Obama Ran Pedophile Ring Out of the White House – The Leaked Email! – https://amg-news.com/wikileaks-bombshell-obama-ran-pedophile-ring-out-of-the-white-house-the-leaked-email/
BOOOM!!! Judy Byington Bombshell Report: Biden, Pelosi, Obama Charged with Treason, Collusion with CCP on 2020 Voter Fraud, Pedophile Ring Run out of the White House – https://amg-news.com/booom-judy-byington-bombshell-report-biden-pelosi-obama-charged-with-treason-collusion-with-ccp-on-2020-voter-fraud-pedophile-ring-run-out-of-the-white-house/
BOOM! Wikileaks CIA Vault 7: The CIA Can Spy Through TVs, IPhones, Smartphones And Windows PCs – The CIA is Hack you Right Now – https://amg-news.com/boom-wikileaks-cia-vault-7-the-cia-can-spy-through-tvs-iphones-smartphones-and-windows-pcs-the-cia-is-hack-you-right-now/
BOOM! DISCLOSURE (Declassified & Authorized): The Truth About Julian Assange & Wikileaks – Julian is Fine – Was a US Mil. Intel. Op – Busted the 2016 Clinton Elections Coup d’Etat . . .https://amg-news.com/boom-disclosure-declassified-authorized-the-truth-about-julian-assange-wikileaks-julian-is-fine-was-a-us-mil-intel-op-busted-the-2016-clinton-elections-coup-detat/
Share on Twitter!














![TOP INTEL ALERT | WAR ROOM BULLETIN — “GENERAL FLYNN WARNS: NATO IS PROVOKING A NUCLEAR CONFLICT — TRUMP MUST ACT” [VIDEO]](https://amg-news.com/wp-content/uploads/2025/06/General-Flynn-NATO-warning-450x239.png)
![OFFICIAL DOCS JUST RELEASED | “OBAMA NAMED IN ADRENOCHROME TRAFFICKING RING — GOVERNMENT DOCS REVEAL HORRIFIC FEDERAL INVOLVEMENT” [VIDEO]](https://amg-news.com/wp-content/uploads/2025/06/OBAMA-NAMED-IN-ADRENOCHROME-TRAFFICKING-RING--450x256.png)
![BREAKING INTEL REPORT | GLOBAL ESCALATION ALERT | “OPERATION SPIDERWEB” – PUTIN ISSUES MILITARY WARNING AFTER UKRAINE STRIKES STRATEGIC BOMBER BASES INSIDE RUSSIA [VIDEO]](https://amg-news.com/wp-content/uploads/2025/06/Putin-threat-after-drone-strike-450x335.jpg)
![BREAKING NEWS | JUNE 3, 2025 | TRUMP’S AMERICA STRIKES HARD: FBI HUNTS THE GENDER BUTCHERS — FEDERAL CRACKDOWN IGNITED TO PROTECT OUR CHILDREN [VIDEO]](https://amg-news.com/wp-content/uploads/2025/06/TRUMPS-AMERICA-STRIKES-HARD-FBI-HUNTS-THE-GENDER-BUTCHERS-450x252.png)

1 Comment
So, since it is illegal for the CIA to operate within the U.S., this info has now put a stop to all of that illegality. Right?
Right???